Today marks the seventh anniversary of this project.
The decline in queries continues. In 2020, the IP address blocklist saw 1.459 billion queries, which is just short of four million a day, down from 1.7B the year before (15% less). The drop was even more marked for the domain name list, going from 1.4B to 457M (1.25M per day). If the same trend continues, by the end of 2021 we might consider the experiment concluded.
Spring clean
All records older than Sunday, August 28, 2016 3:59:25 PM have been purged. The reason for this is simply the number of records causing issues with the outsourced DNS distribution.
On inclusion and terminology
ScientificSpam DNSBL has always considered itself a blocklist.
Continue reading
Can you de-escalate a listing?
We get delisting requests from hosting providers for whose networks we have escalation listings. Sometimes they are asking for the escalation to be removed in favour of targeted listings for the spammer, implying that they’re okay hosting the spammer even though they understand why we listed them.
Please write in in plain text
We get email that starts with
<html xmlns:o="urn:schemas-microsoft-com:office:office" xmlns:w="urn:schemas-microsoft-com:office:word" xmlns:m="http://schemas.microsoft.com/office/2004/12/omml" xmlns="http://www.w3.org/TR/REC-html40"><head><meta http-equiv=Content-Type content="text/html; charset=utf-8"><meta name=Generator content="Microsoft Word 15 (filtered medium)"><style><!--
and all we can say is please adjust your email program so we can read what you wanted to say. That is, if you want us to read it and react to it.
Public notice to Web Werks Pvt Ltd [EnterpriseDCTAC #CAV-139-41061]
We have already once commented in public on this website (see earlier article) about the difficulty of communicating with you when you write in from a ticket system. This is just a heads-up; we have responded to you. If you don’t see our response, it’s not our fault. If you expect us to respond in your ticket system rather than in e-mail, don’t hold your breath.
Mar 5 11:31:39 x postfix/smtp[21423]: 89B9413E055: to=[email protected], relay=aspmx2.spamshooter.com[206.183.104.6]:25, delay=203, delays=0.05/0.04/200/3.1, dsn=2.0.0, status=sent (250 OK id=1j9oj3-0000Gh-CZ)
And as for the issue itself:
- Our services are not used by Yahoo, Hotmail and Gmail.
- Your RFC 5322 noncompliance issues are not related to Scientific Spam DNSBL listings and cannot be fixed by Scientific Spam.
- Get rid of OMICS.
Happy Birthday, Scientific Spam
It is already six years and a day since we started operations.
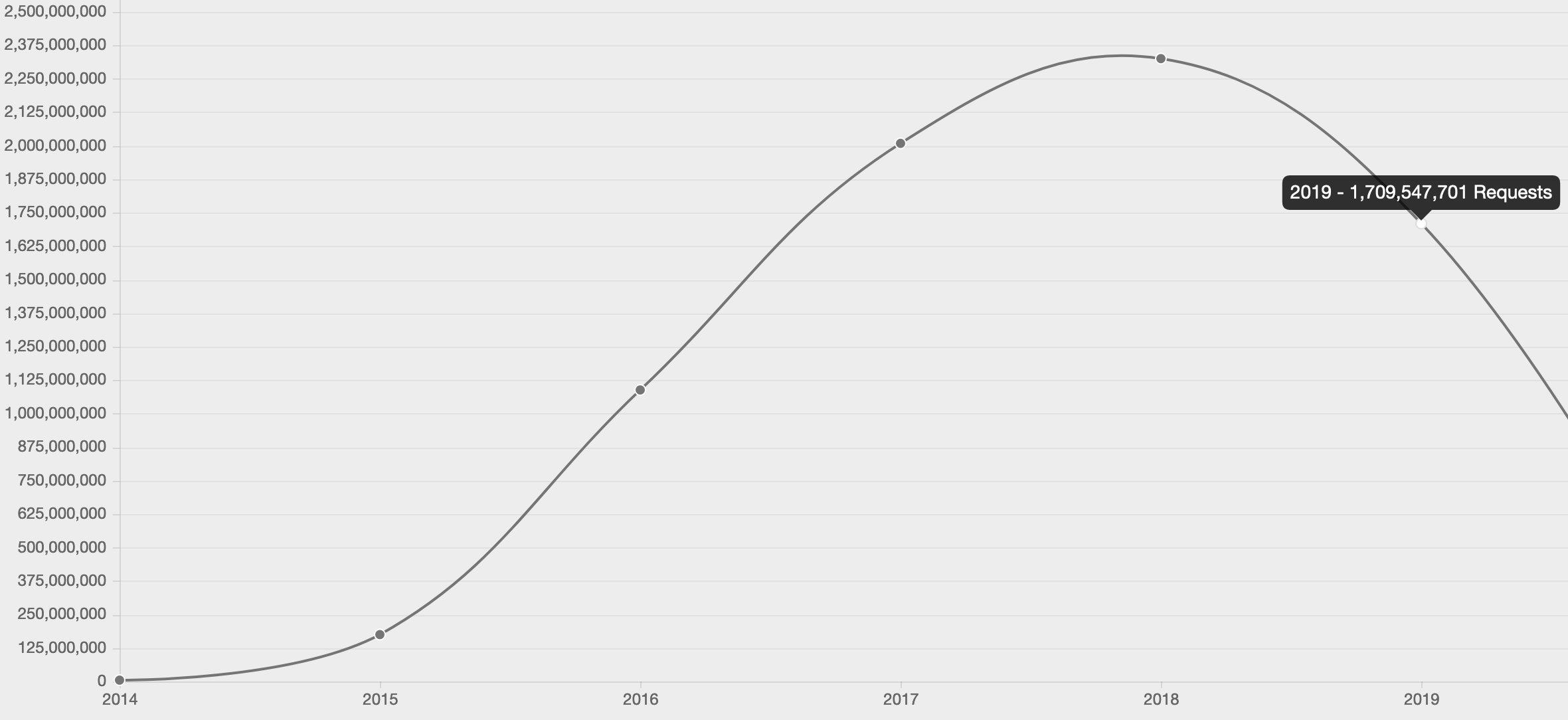
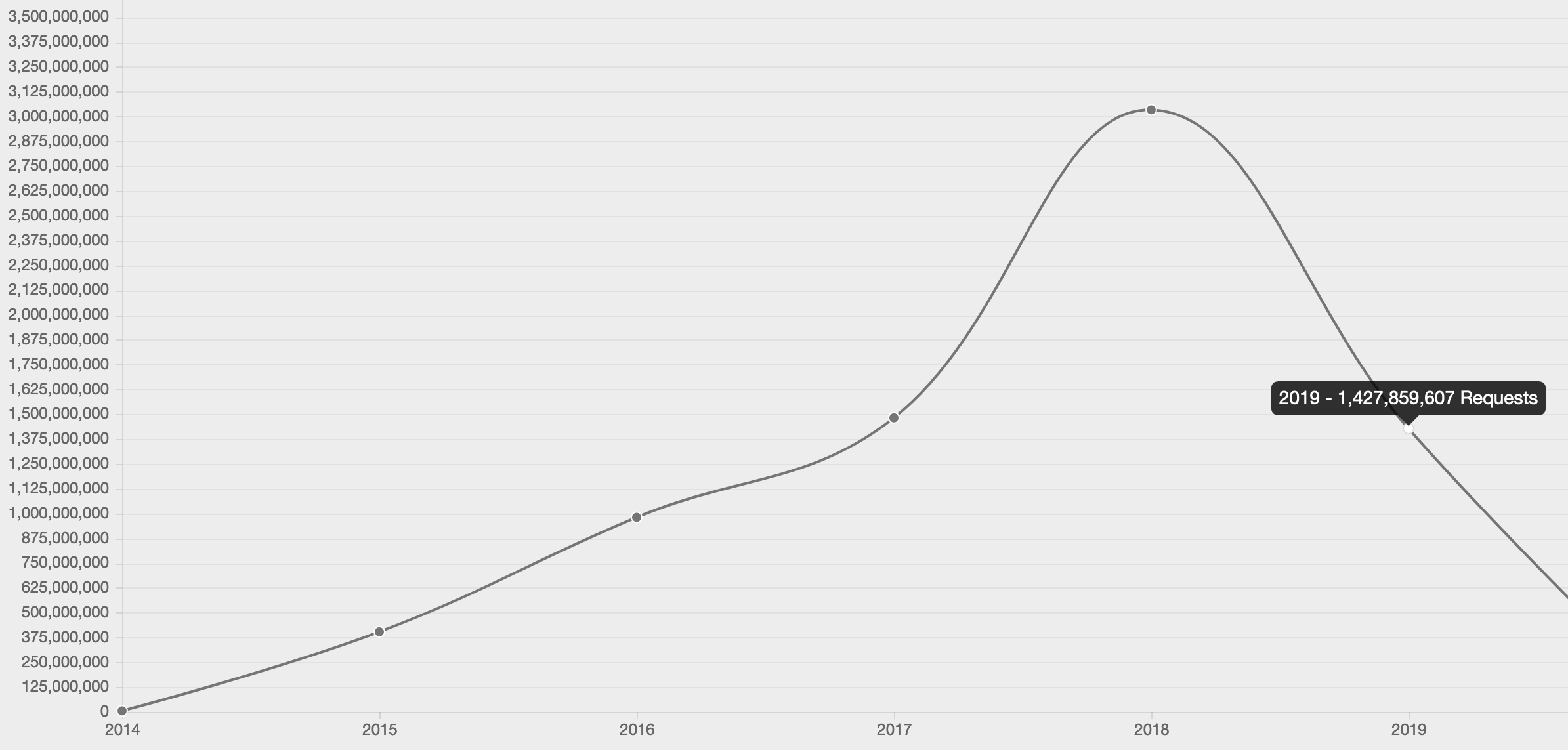
Usage has gone ~25% down on the IP list, with 1.7 billion queries recorded in 2019 (over 2.3 in 2018). The decline is even more marked on the right-hand side list, with 1.4B in 2019 compared to over 3B in 2018.
As always, thank you to everybody who is querying the data. If you have any suggestions, the usual email address is listening.
Our spam is not spam
Private email addresses never gets registered without the individuals consent however public addresses are registered, which our legal department has assured us is perfectly legal.
We love honest admissions of being spammers, especially when the spamming company includes a CC to their own email service provider.
Public notice to MailKitchen
We replied to you on October 24, 2019, and again on Nov 5 (if only to indicate that we had already replied). You keep sending in new messages that don’t indicate you’ve seen any reply from us. We keep deleting the new messages. If you want to have a conversation, you need to have a conversation, and that means reading our replies and responding to them.
Public notice to Server Wala
We keep deleting your new messages that contain no new information.
Respond to Message-ID: <20190826103442.GF18782 at crick.scientificspam.net> if you want a response.